The SecurityFocus web sites have been running a series of articles on web browser security. The articles target the two major browsers, IE (6 and 7) and (strangely) older versions of Firefox (1.5 and 2.0). The current article looks at attacks on Password Managers. The user is given a false sense of security because they "expect that the browser, possibly in conjunction with the operating system, will protect their information". The significant take away was that these browsers are not to be trusted to store personal information such as usernames, passwords and other stored form information.
Firefox's password manager (version 2.0) as of November 2006 has a software flaw that allows a user's credentials (from the site is currently visited) to be posted to any URL if the user clicks a maliciously crafted link.
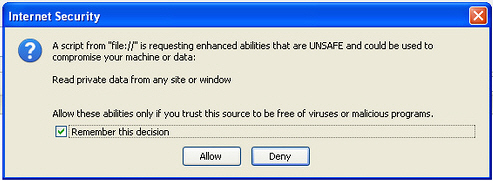
And IE( 6 or 7) has this issue:
Internet Explorer is usually a prime target for malware infection. These vulnerabilities converge at a dangerous point where malware programs are specifically targeting AutoComplete information. These programs gain confidential information and then send it back to the attacker.
So what we do to reduce the risks? Fortunately, the article provides some defensive strategies. They suggest avoiding password managers altogether, using a strong ( not easy guessed ) password to protect the password manager, using an alternative password manager that supports encryption, strong and unique passwords for every site, and even some programming tips for web developers.
On my Mac, I use 1Password. 1Password uses a master password, encrypts stored passwords and form data, and can generate unique random passwords for any site. You can Download 1Password here and give it a test drive.
Check out this article on the The Real Life Risks Of Re-Using The Same Passwords.
